DISCOVER ALL YOUR DATA
Gain complete visibility of sensitive data across your network
comforte Data Security Platform
POLICY
PROTECT
INTEGRATE
AUTOMATION
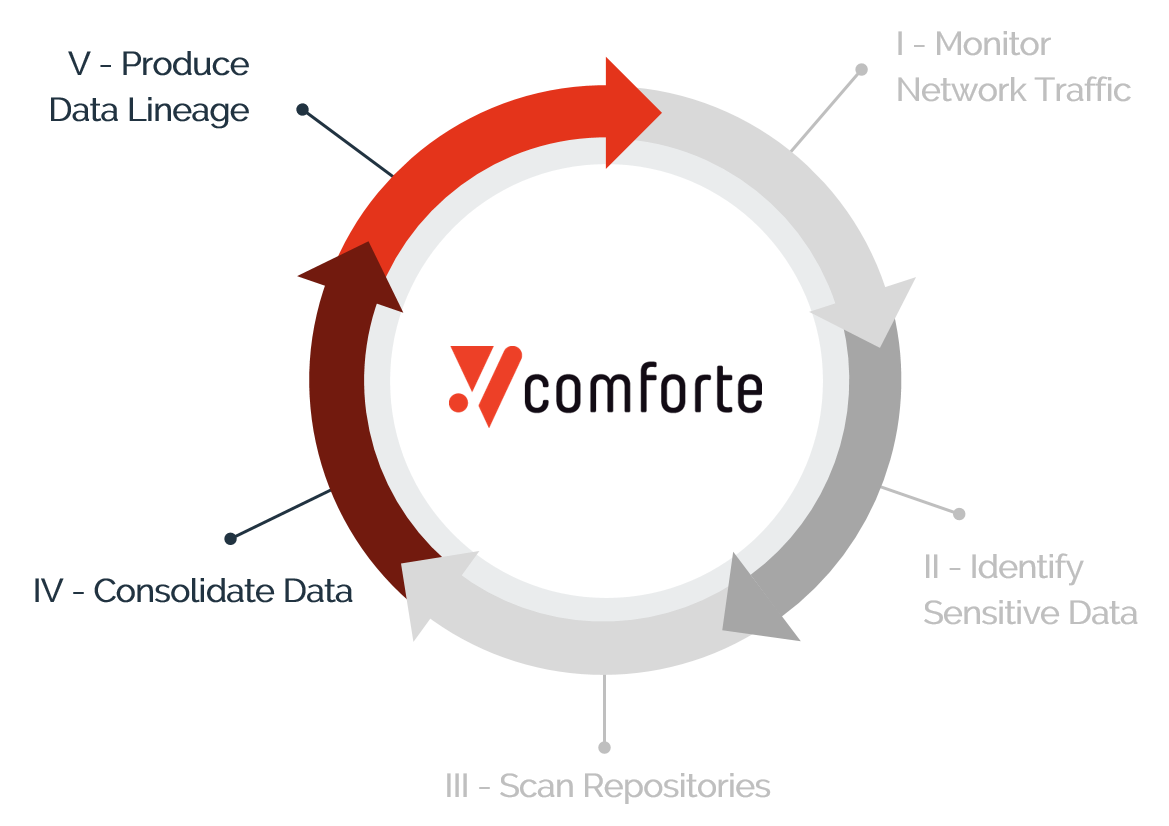
Through a continuous passive network packet capture process, we identify sensitive data (i.e., highly-regulated PII) flowing through the organization.
This data flow visibility enables us to identify repositories (including new or unknown ones) with sensitive data.
Comprehensive scans of those repositories give you full visibility into your data environment - without the need to deploy any agents.
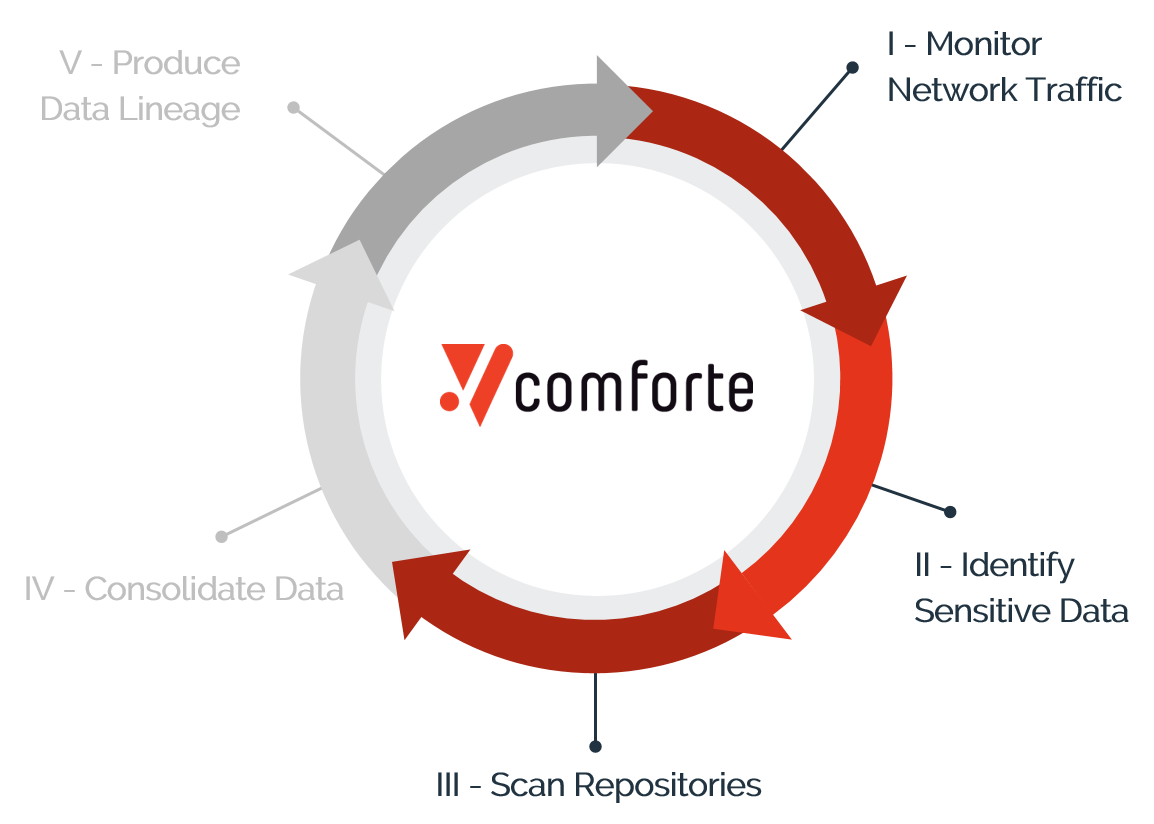
Catalogue and organize all discovered data to understand business context, data lineage & history.
This automated process ensures that you always have access to the most current information about PII in your environment, allowing you to respond to data subject access requests (DSAR), and many other privacy, security, and data governance purposes.
Once you find your sensitive data, how do you protect it?
Besides discovery, the ability to instrument data protection in a consistent manner at scale provides total control over sensitive data, wherever it goes. This facilitates cloud migration, SaaS adoption, AI/ML initiatives, and other high-value activities involving sensitive data.
Learn more about Protection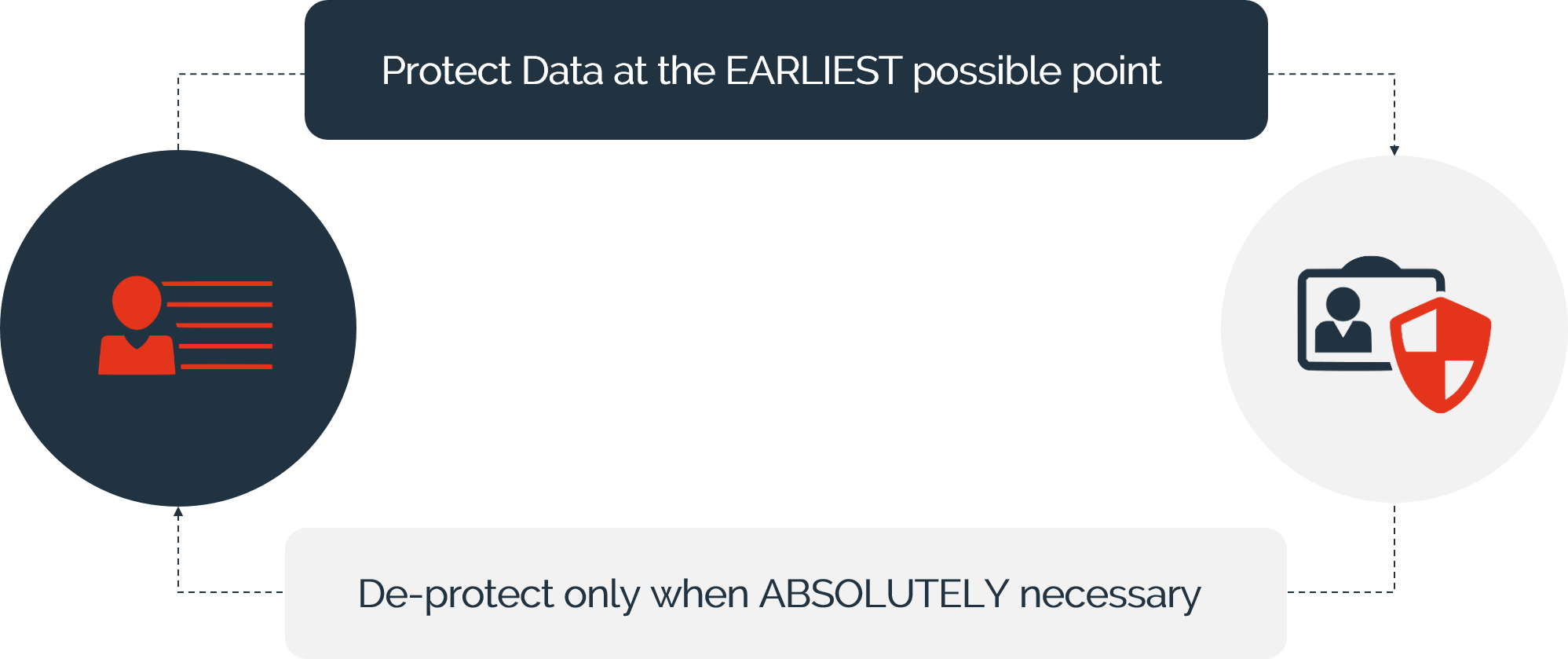
Fortune 500 insurer automates data discovery
- Automated, continuous data discovery & classification
- Integration with Microsoft 365 E5 and existing DLP and GRC tools
- Deeper discovery and improved policy enforcement
- Reduction of manual efforts