One Platform to Modernize and Secure HPE Nonstop
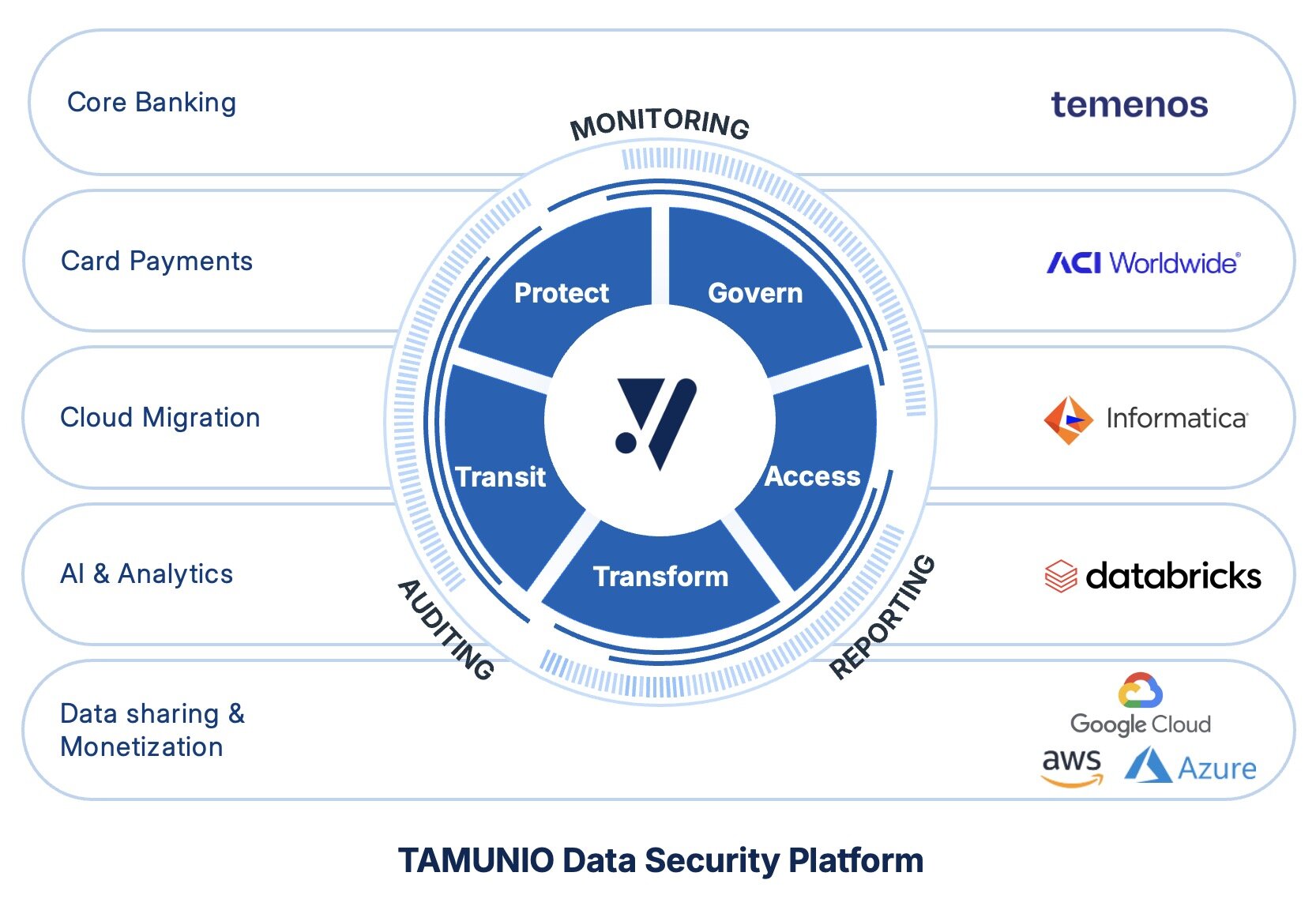
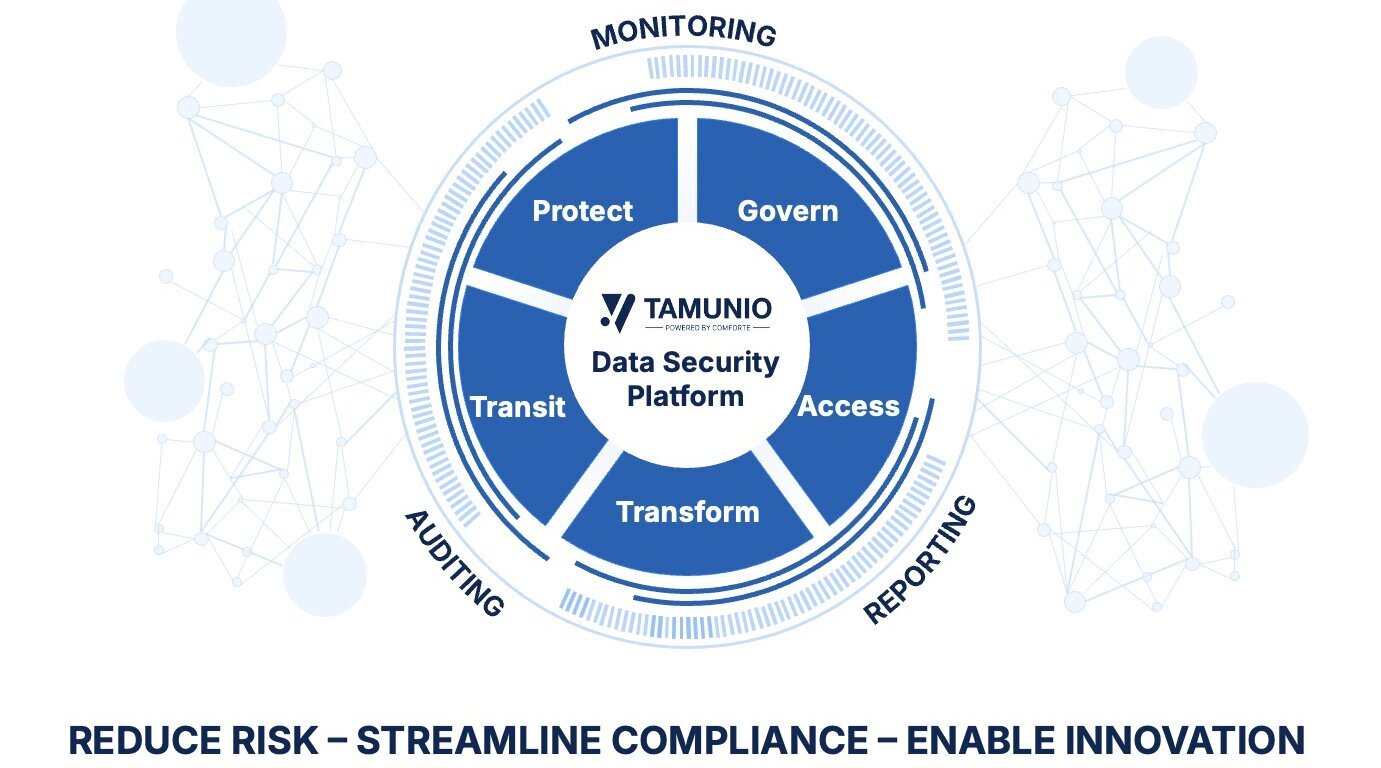
Secure mission-critical data on HPE Nonstop and hybrid enterprise systems. TAMUNIO unifies keys, secrets, and advanced protection for APIs, analytics, and secure cloud adoption.
Explore the TAMUNIO platformWhy HPE Nonstop Needs an Upgrade
HPE Nonstop supports payments, banking, retail, and telecom at scale. But today’s requirements go beyond reliability as organizations look to modernize and embrace the cloud and AI. TAMUNIO unifies protection, compliance, and observability across HPE Nonstop and enterprise systems so you can modernize without exceptions.
Tomorrow’s Data Security, Delivered Today
TAMUNIO provides a pragmatic path: start with high-impact controls, minimize change risk, and extend the same policies enterprise-wide when you’re ready. From one platform, standardize keys and certificates, apply data protection that fits existing schemas, and centralize monitoring for faster evidence and smoother operations.
How Discover’s PULSE Network Met PCI Requirements on HPE Nonstop
A national debit network needed to protect payment data under new PCI DSS requirements on a tight timeline without disrupting operations on HPE Nonstop.
- Rapid rollout: 3-month POC; full deployment the same year
- Easy adoption: across settlement, fraud, and reporting
- Performance: robust security with reported zero-latency impact
What TAMUNIO Delivers
Data Protection
- Protect sensitive data in place (format-preserving, file-level)
- Automate key/certificate lifecycles
- Prepare for post-quantum cryptography
Digital Enablement
- Open core HPE Nonstop services via secure APIs and modern UIs
- Enable analytics/AI with de-identified, format-preserved data
Connectivity
- Standardize TLS/SSH with certificate automation
- Move data securely with high-throughput transfers
"Comforte has been a valuable partner for our data protection needs. Their expertise in this domain has provided us with proven, effective solutions that are compatible with our internal systems and software. We appreciate their partnership, collaboration, and expertise in this area."
Stephanie Stamos, Director of Technology Services at Discover
How TAMUNIO Helps Teams
For Business & Product Teams
Turn HPE Nonstop reliability into a competitive advantage with faster delivery, lower risk, and smoother collaboration across the enterprise.
Deliver new features faster, leveraging real Nonstop data safely for dev/test.
Protect customer trust, keep sensitive fields unreadable during analytics and processing.
Safely accelerate partnerships, share services without risk or delay.
For Security & Compliance Leaders
Shorter audit cycles, clearer accountability, and a stronger, more consistent security posture across HPE Nonstop and enterprise IT.
Unify logs, identity, and access—faster, easier audits.
Enforce MFA/SSO, centralized KMS, and prove quantum-resilience for long-lived records.
For HPE Nonstop Operations
Lower operational risk, and consistent controls that don’t slow the platform.
Transparent protection for files, tapes, and backups.
Standardize access, TLS/SSH, and monitoring from one place.
For Architects
Nonstop remains the reliable core while securely participating in hybrid, analytics, and AI initiatives.
Extend Nonstop securely into hybrid analytics and AI.
Clean SIEM/IAM/data platform integration, one policy from core to cloud.
Why It’s Time to Modernize and How TAMUNIO Responds
Impact That Matters
| Challenge | With TAMUNIO |
|---|---|
| Be audit-ready, faster | ✔ Centralize evidence and export standardized events to your SIEM. |
| Reduce key & certificate concerns | ✔ Automate lifecycles, prevent outages. |
| Smaller PCI/PII scope | ✔ Keep sensitive fields de-identified on HPE Nonstop and across the enterprise. |
| Low-risk modernization | ✔Layer controls without changing apps, preserve formats/protocols. |
FAQ
Do we need to change or rewrite our HPE Nonstop applications?
Typically, no. TAMUNIO layers controls (keys, protection, auditing) without breaking formats or workflows.
How does TAMUNIO speed compliance?
Unified logging, monitoring, and SIEM exportation means evidence is always ready.
What’s the Key Management Service (KMS) for HPE Nonstop?
The KMS Automates all trust processes (keys, certificates, SSH/MFA), minimizing manual work and risk.
Will this impact HPE Nonstop performance?
Controls are designed for mission-critical environments. The exact impact depends on your use cases and volumes.
Can HPE Nonstop protections extend to cloud, analytics, and AI projects?
Yes. Policies and protections can be applied consistently as data moves to enterprise systems and cloud services, preserving format/structure where needed for downstream use.
I’m a current comforte customer, how do I upgrade to TAMUNIO?
We’ll work with you to map your current solution to TAMUNIO and guide you through the upgrade process. Contact your comforte account team to get started.
